Why Offboarder?
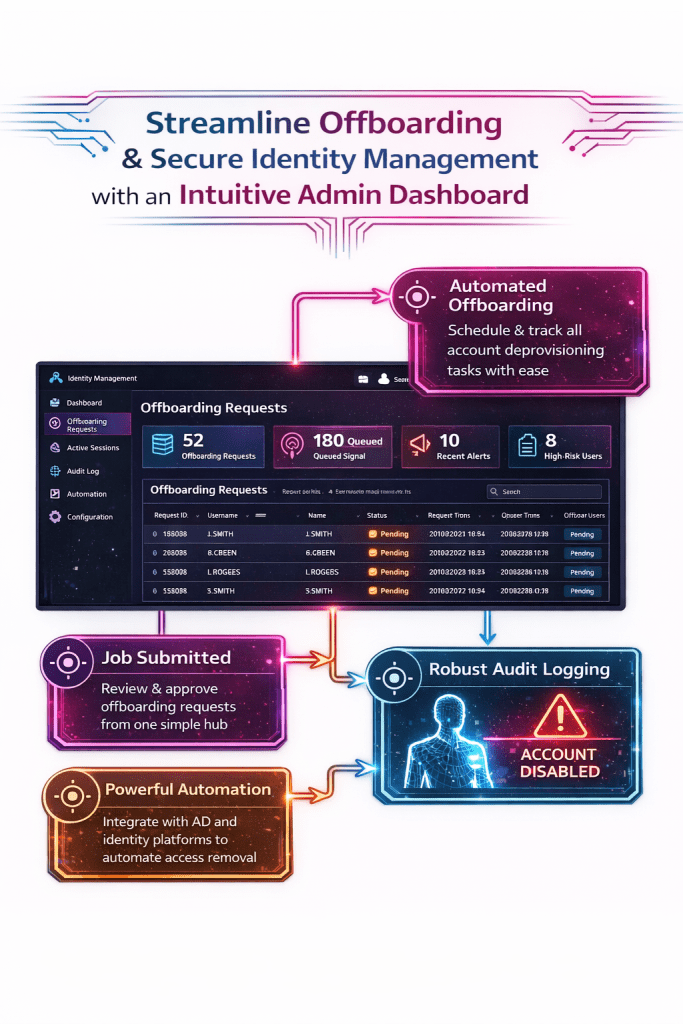
Offboarder makes offboarding timely and consistent by turning access removal into a repeatable, auditable process rather than a manual checklist. It delivers evidence you can trust—complete and accurate logs that stand up to audits and customer security reviews. And it does this without the cost and complexity of heavyweight, highly customized alternatives, reducing operational overhead while lowering risk.
Why it matters.
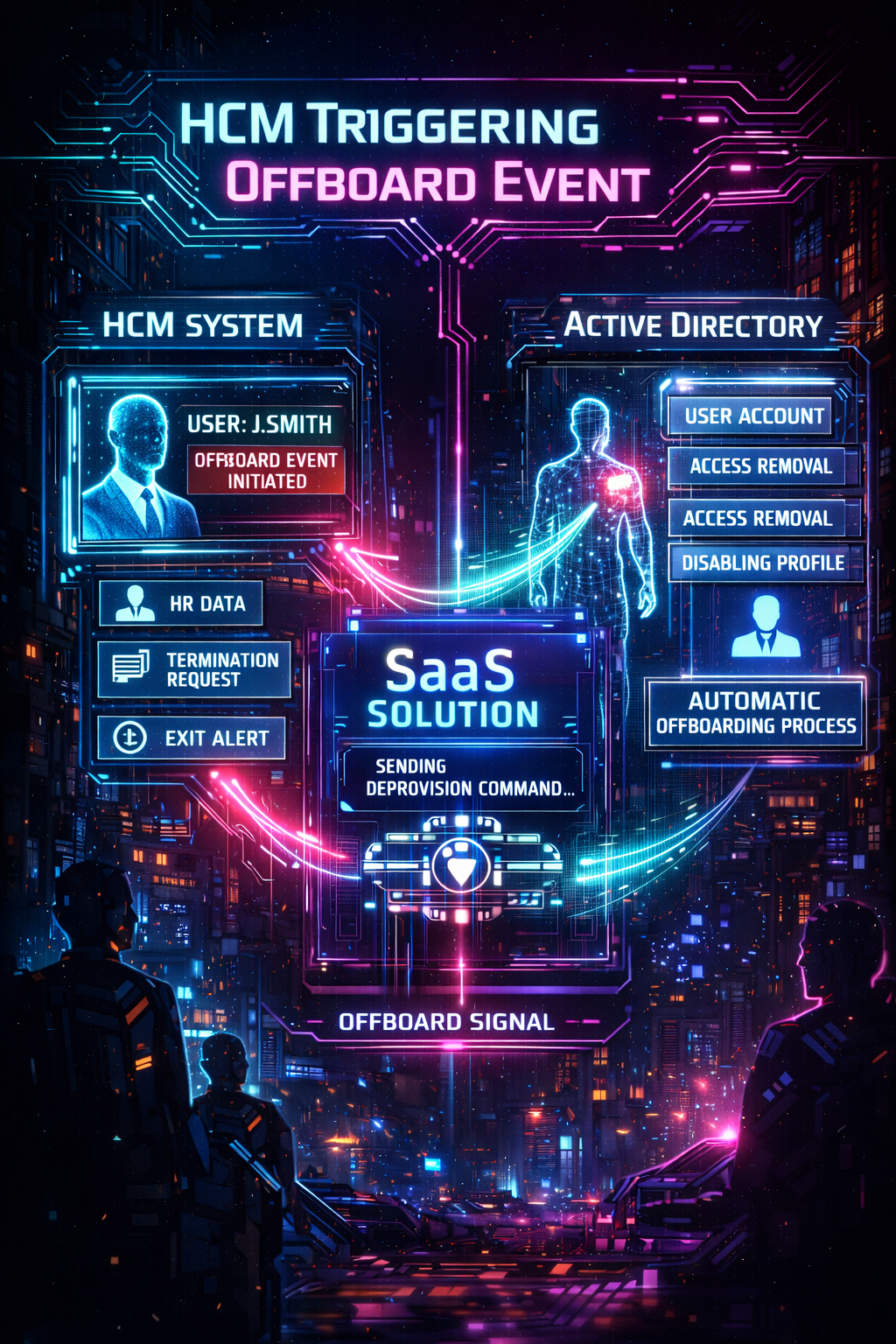
Terminating logical access quickly after a role change or termination is one of the highest-impact controls for reducing breach risk and audit findings, because the most common failure mode is lingering access (orphaned accounts, unrevoked group membership, and leftover privileges).
That’s why frameworks and regulations consistently test access governance and deprovisioning—including ISO/IEC 27001, SOC 2, SOX ITGC, HIPAA Security Rule, PCI DSS, and NIST-aligned programs—looking not just for policy, but for evidence that access was removed promptly and consistently.
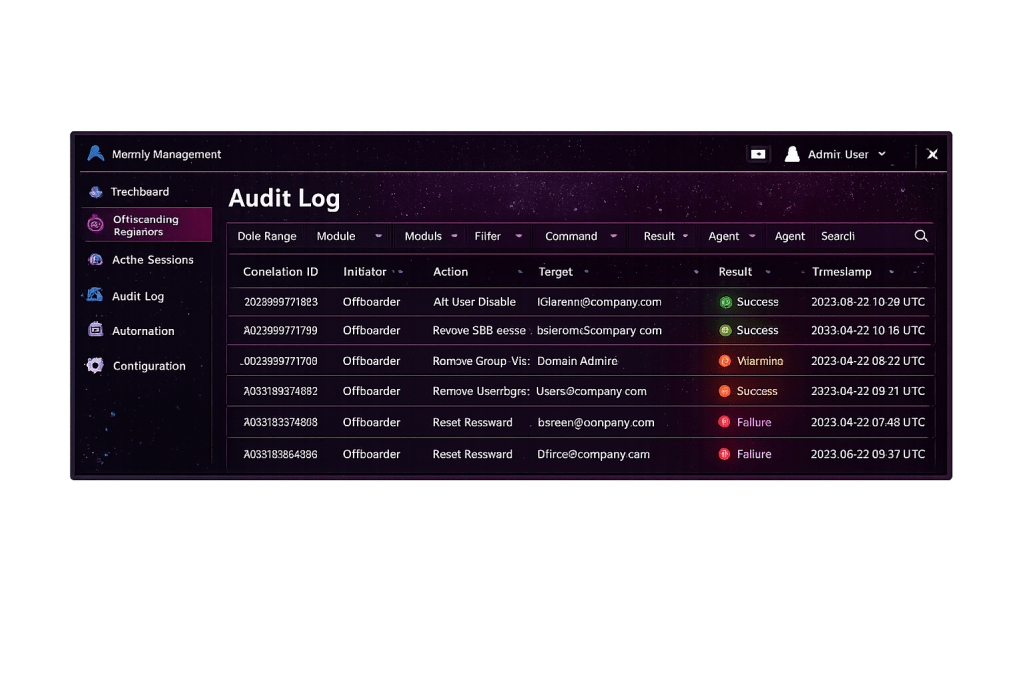
Completeness and Accuracy (C&A) of logging is critical: completeness proves you captured every offboarding event and every affected system, and accuracy proves the timestamps, identities, approvals, and outcomes are correct and traceable—so audits, incident investigations, and customer security reviews don’t collapse into “we think it happened.” Many alternative solutions become costly because they introduce heavy customization, broad identity program overhead, and ongoing manual coordination to reconcile gaps in evidence—driving recurring labor, longer offboarding times, and repeat remediation cycles.
Security by Design
Offboarder makes offboarding timely and consistent by turning access removal into a repeatable, auditable process rather than a manual checklist. It delivers evidence you can trust—complete and accurate logs that stand up to audits and customer security reviews. And it does this without the cost and complexity of heavyweight, highly customized alternatives, reducing operational overhead while lowering risk.