Ghost accounts represent one of the most persistent and dangerous vulnerabilities in modern enterprise IT environments. These dormant or orphaned user identities persist long after an employee, contractor, or partner has left the organization. For Governance, Risk, and Compliance (GRC) managers, ghost accounts are more than just a security nuisance; they are a direct indicator of a failing identity governance program.
The presence of unauthorized access pathways violates the principle of least privilege and creates significant exposure during regulatory audits. Manually tracking every departure across a fragmented SaaS landscape is no longer a viable strategy for risk mitigation. To ensure security and maintain compliance with frameworks like SOC 2 and ISO 27001, organizations must leverage Identity and Access Management (IAM) automation to systematically detect and remove these accounts.
The Critical Role of Ghost Accounts in Compliance Failures
Ghost accounts often stem from a breakdown in the communication chain between HR and IT. When a termination occurs, the primary directory might be updated, but downstream applications often retain active credentials. This creates a "control gap" that auditors specifically look for during logical access reviews.
Under ISO 27001 and SOC 2, organizations are required to demonstrate that access is revoked in a timely manner. A single orphaned account found during a sample test can lead to a qualified audit report or a formal finding. These accounts are attractive targets for attackers because they are rarely monitored, making unauthorized activity difficult to detect until a breach has already occurred.
Automating the removal process transforms access cleanup from a reactive, manual scramble into a consistent, tamper-resistant workflow. This shift ensures that every identity is accounted for and every exit is documented with precision.
The Mechanics of IAM Automation
IAM automation tools function by creating a unified view of the identity lifecycle. Instead of relying on IT staff to remember to log into twenty different portals, the platform orchestrates the deprovisioning process across the entire stack.
Automated Detection Across the SaaS Landscape
Modern automation tools scan primary directories, such as Azure AD or Okta, alongside connected SaaS applications like GitHub, Salesforce, Slack, and Jira. The system identifies accounts that no longer have a corresponding active record in the Human Resources Information System (HRIS). This cross-referencing ensures that even if an IT ticket is missed, the automation layer catches the discrepancy.
Risk Prioritization and Scoring
Not all ghost accounts carry the same level of risk. An orphaned account with administrative privileges in a production environment is a critical emergency, while a dormant account in a low-sensitivity communication tool is a lower priority. Automated tools score these accounts based on inactivity duration, privilege level, and the sensitivity of the data they can access.
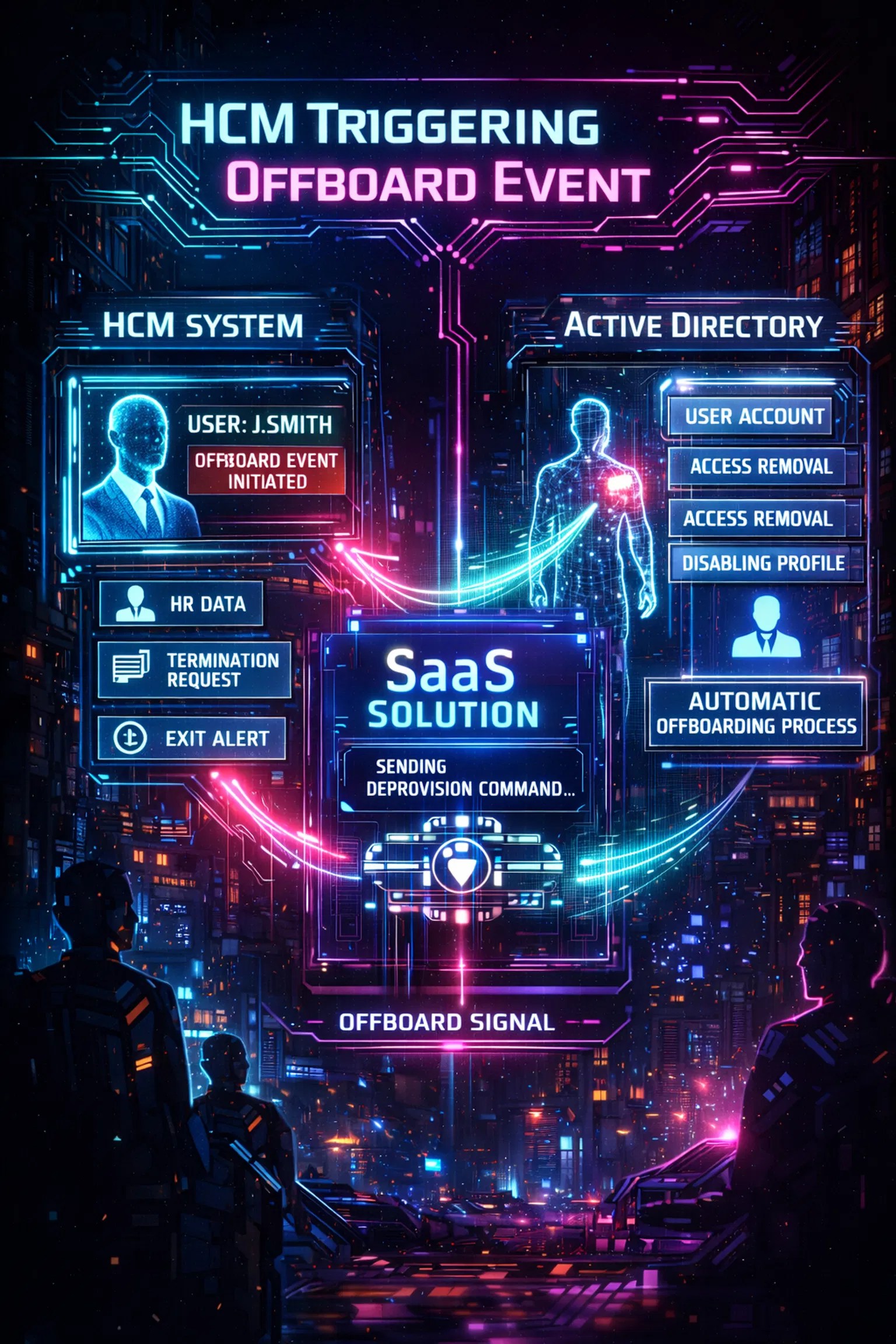
The Critical Role of HR Integration
The foundation of a secure identity program is the "Golden Source" of truth, which is almost always the HR system. When an employee’s status changes to "Terminated" in systems like Workday, BambooHR, or Visma, the IAM platform should trigger an immediate response.
By utilizing the SCIM (System for Cross-domain Identity Management) protocol, the platform can instantly revoke access across all supported applications. This eliminates the latency period between an employee leaving the building and their digital access being severed. For GRC managers, this integration provides the "evidence capture" necessary to prove that termination controls are functioning as intended.
Failure to integrate HR data into the IAM workflow often results in "zombie" accounts that linger for months or years. These accounts represent a significant operational risk that can only be mitigated through deep technical integration. You can learn more about why termination of access controls matters to better understand these risks.
Detection and Risk Prioritization

Once the integration is established, the platform begins the process of continuous monitoring. It identifies accounts that meet specific "cleanup criteria," such as:
- Accounts inactive for more than 90 days.
- Accounts not associated with an active employee or contractor ID.
- Accounts created outside of the standard provisioning workflow.
By flagging these accounts automatically, the GRC team can focus on remediation rather than discovery. The platform provides a centralized dashboard where all orphaned identities are visible, categorized by their potential impact on the organization’s security posture. High-risk accounts are escalated for immediate action, while lower-risk accounts can be handled through automated batch processing.
Automated Remediation and Exception Handling
Automation does not always mean immediate deletion. In many corporate environments, certain accounts must be preserved for legal discovery or data retention purposes. A sophisticated IAM tool allows for policy-defined remediation steps.
For example, a policy might dictate that an account inactive for 180 days is automatically disabled, but not deleted, for an additional 30 days. This "safety buffer" prevents accidental data loss while still neutralizing the security threat. If the system encounters an ambiguous case: such as a service account that appears dormant but is actually critical for a legacy process: it can automatically generate a Jira ticket for manual review.
This hybrid approach ensures that nothing falls through the cracks. Every action taken by the platform, and every decision made by a human reviewer, is logged in a tamper-evident audit trail. This level of security and compliance is essential for meeting modern regulatory demands.
Architecture of an Automated System
Implementing an automated solution requires a clear understanding of the technical architecture involved. A robust system typically involves a secure connection between the on-premises environment (if applicable) and a cloud-based management portal.

The architecture shown above illustrates how a cloud-based agent can bridge the gap between local domains and SaaS applications. This setup allows for the centralized management of identities regardless of where the resources reside. By consolidating these controls, the organization reduces the "surface area" that an attacker can exploit.
For many organizations, the move toward automated deployment of these tools is the quickest path to achieving a mature security posture. Centralized architecture simplifies the enforcement of security policies and ensures that audit logs are consistent across the entire enterprise.
Achieving Audit Readiness
For a GRC manager, the ultimate goal of IAM automation is audit readiness. During a SOC 2 or ISO 27001 audit, the auditor will ask for proof that access is reviewed and revoked. Manual spreadsheets are difficult to verify and easy to manipulate.
Automated systems provide "point-in-time" reports and historical logs that serve as definitive evidence of control performance. These reports demonstrate:
- Consistency: Every employee is treated the same way upon departure.
- Timeliness: Access is removed within the required SLA (often 24 hours).
- Accuracy: There are no lingering accounts in downstream systems.

Using an automated platform turns the audit process from a stressful event into a routine demonstration of operational excellence. Instead of spending weeks gathering data, the GRC team can generate a compliance report in minutes. This efficiency allows the team to focus on higher-level governance tasks rather than manual data entry.
The Financial Benefit: Reclaiming License Waste
Beyond security and compliance, there is a clear financial incentive for eliminating ghost accounts. Every orphaned account in a SaaS application like Salesforce, Microsoft 365, or Zendesk represents a recurring cost.
IAM automation tools often include license management features that identify unused or underutilized seats. By automatically deprovisioning these accounts, the organization can reclaim significant portions of its IT budget. In many cases, the cost savings from license reclamation alone can justify the investment in an IAM automation platform.
Reducing "license bloat" also simplifies the IT environment. Fewer active accounts mean fewer entries to manage, fewer passwords to reset, and a smaller overall risk profile. Efficiency in license management is a hallmark of a well-governed organization.
Implementing the Strategy
To begin leveraging IAM automation, GRC managers should follow a structured implementation path:
- Audit the Current State: Identify where the current offboarding process is failing and where ghost accounts are most likely to hide.
- Define Cleanup Policies: Establish clear rules for when an account should be flagged, disabled, or deleted.
- Enable SSO: Ensure as many applications as possible are behind a Single Sign-On provider to centralize access control.
- Integrate HR and IAM: Connect the HR system to the automation platform to create a seamless trigger for deprovisioning.
- Monitor and Iterate: Use the platform’s reporting features to continuously improve the process and address new risks as they emerge.
The transition to automated identity governance is an essential step for any organization operating in a high-stakes regulatory environment. By eliminating ghost accounts, GRC managers can significantly reduce operational risk and ensure that their organization remains secure and compliant.
For more information on why these tools are becoming the industry standard, explore our insights on why identity governance tools exist. Automation is not just a convenience; it is a fundamental requirement for modern cybersecurity governance. Strong logging and automated workflows help turn daily activity into long-term accountability.

Leave a Reply