Manual offboarding is a significant operational liability for modern enterprises. Relying on spreadsheets, email chains, and human memory to revoke system access creates a dangerous control gap. This fragmentation often leads to orphaned accounts that remain active long after an employee has departed.
Organizations must prioritize automated offboarding workflows to maintain a robust security posture. By shifting from manual checklists to orchestrated automation, businesses can ensure that access termination is immediate, consistent, and fully documented. This approach is no longer optional for companies aiming to meet rigorous global security standards.
The primary objective of offboarding automation is to eliminate the risks associated with human error. When an IT administrator misses a single application during a manual exit process, the organization remains vulnerable to unauthorized access. Automation provides a tamper-resistant path to security that scales with the business.
The Critical Role of IAM Compliance
Identity and Access Management (IAM) compliance focuses on ensuring the right individuals have access to the right resources at the right time. During an employee exit, the focus shifts to the timely removal of that access. Regulators and auditors view the speed and accuracy of this removal as a primary indicator of organizational maturity.
Standards like ISO 27001 and SOC 2 require strict evidence that logical access controls are functioning as intended. A failure to provide timestamped proof of account deactivation can lead to failed audits and lost certifications. Why termination of access controls matters more than you think is a fundamental concept for any compliance-focused leadership team.
Automated systems generate the necessary audit trails automatically. Every action taken by the workflow: from disabling a directory account to revoking a SaaS license: is logged in a centralized repository. This evidence capture transforms a high-risk administrative burden into a predictable compliance asset.
Core Components of an Automated Workflow
An effective offboarding workflow must go beyond simply disabling an email account. It should encompass the entire digital footprint of the departing user. This includes modifying passwords, transferring document ownership, and reallocating email aliases to ensure business continuity.
Access revocation must happen across all layers of the technology stack. This includes on-premises directory services, cloud-based productivity suites, and niche third-party applications. Without a unified workflow, these disparate systems often fall through the cracks of a manual process.
License deallocation is another critical component that directly impacts the bottom line. Automated workflows identify unused licenses in real-time, allowing organizations to reclaim and reallocate resources. This efficiency reduces unnecessary software spend while maintaining a lean operational profile.

Strategic Implementation: A Step-by-Step Guide
The first step in implementing automation is to map the current offboarding process. Organizations must identify every stakeholder involved, from HR and IT to finance and department managers. Mapping the flow of information helps pinpoint existing bottlenecks and technical dependencies.
High-risk tasks should be prioritized for immediate automation. These are typically tasks that involve administrative privileges or access to sensitive customer data. Resolving these "low-hanging fruit" vulnerabilities provides immediate risk mitigation and demonstrates the value of the platform to stakeholders.
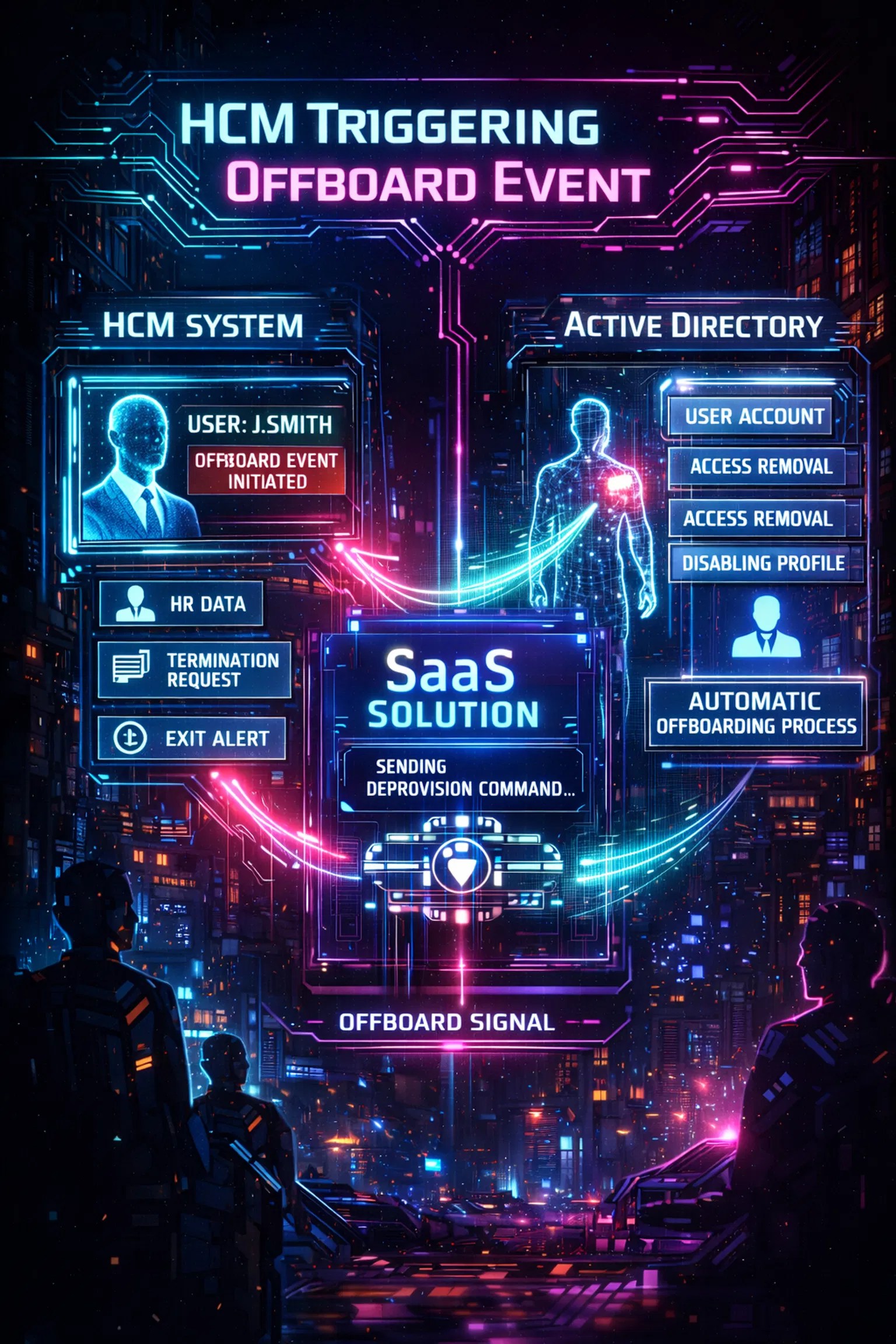
The third step involves selecting a platform that integrates with existing HR Information Systems (HRIS). A seamless connection between HR data and IT actions ensures that the workflow is triggered the moment an employee's status changes. This "HR-to-IT" bridge is the foundation of a modern identity governance strategy.
Enhancing Security Through Immediate Revocation
The window of time between an employee's departure and their access removal is a period of peak vulnerability. Malicious actors or disgruntled former employees can exploit this gap to exfiltrate data or disrupt services. Automation closes this window by executing deprovisioning commands in seconds rather than days.
Why secure offboarding matters is best understood when looking at the speed of modern cyber threats. A manual process that takes 24 hours is no longer sufficient in an era of automated attacks. High-speed revocation is a prerequisite for a resilient security architecture.
Time-delayed execution can also be programmed into these workflows for specific scenarios. For example, a manager might require temporary access to a former employee's inbox for 30 days. The automated system can grant this access and then automatically revoke it, ensuring no permanent access creep occurs.

Meeting ISO 27001 and SOC 2 Requirements
Compliance frameworks place a heavy emphasis on "proof of execution." It is not enough to say that access was removed; the organization must prove exactly when and how it happened. Automated workflows provide this proof through detailed activity logs that are difficult to replicate manually.
ISO 27001 specifically requires organizations to manage the return of assets and the removal of access rights upon termination. An automated platform tracks these requirements as part of a standardized workflow. This consistency ensures that the organization remains audit-ready at all times.
SOC 2 audits examine the effectiveness of logical access controls over a period of time. Manual processes are prone to "point-in-time" failures that can disqualify an entire audit period. Automation maintains a steady state of compliance, reducing the stress and cost associated with annual audit cycles.
Managing Technical Debt and Legacy Systems
Many organizations struggle with legacy systems that do not offer modern API connections. This technical debt often becomes an excuse for maintaining manual offboarding processes. However, a modern automation platform can bridge the gap between on-premises domains and cloud services.
By using secure agents to communicate with on-premises directories, organizations can bring legacy infrastructure into the automated fold. This ensures that even the oldest parts of the network are protected by modern governance standards. Consistency across the entire environment is the only way to eliminate security silos.
What is Offboarder provides clarity on how these hybrid environments are managed. Integrating these tools allows IT teams to focus on strategic projects rather than repetitive administrative tasks. Solving the problem of technical debt is a vital step toward long-term operational stability.
Reducing Operational Risk and Human Error
Operational risk is often the result of complex processes being handled by lean teams. When IT staff are overworked, the secondary steps of offboarding: like device recovery and license reclamation: are often ignored. Automation ensures these steps are completed every time, regardless of team capacity.
Human error is the leading cause of data breaches in many corporate environments. A simple typo in a user directory can leave a backdoor open for unauthorized entry. Workflows eliminate these errors by using programmatic logic to handle data transfers and account modifications.
The platform ensures that every action is repeatable. Whether an organization is offboarding one employee or one hundred, the process remains identical. This predictability is the cornerstone of a secure and compliant business environment.
Leveraging Automated Deployment for Speed
The speed of implementation is a critical factor for organizations facing upcoming audits. Automated deployment allows companies to stand up secure workflows in a fraction of the time required for traditional software. This rapid time-to-value is essential for mitigating immediate risks.
Small teams can leverage these pre-built templates to achieve enterprise-grade security without a massive headcount. By focusing on configuration rather than custom coding, IT departments can secure their environments quickly. Speed in deployment leads to faster risk reduction across the enterprise.
For startups and growing companies, the free 30-day offboarding pilot offers a way to test these controls without upfront capital. Strengthening logical access controls early in a company's lifecycle prevents the accumulation of security debt. Early adoption sets the standard for future growth and governance.
Conclusion: Turning Activity into Accountability
Mastering IAM compliance through offboarding automation is a strategic necessity. It moves the organization from a reactive stance to a proactive, governance-first model. This transition reduces operational risk, ensures compliance, and protects the organization’s most sensitive data.
The transition from manual to automated processes provides the proof of security that modern stakeholders demand. By centralizing the exit process, companies can ensure that no account is left active and no license is wasted. Every automated action contributes to a more secure and auditable infrastructure.
Reliable offboarding is the final, crucial step in the identity lifecycle. Organizations that master this process demonstrate a commitment to security, efficiency, and professional governance. Strong logging and automated triggers help turn daily activity into long-term organizational accountability.

Leave a Reply