
Maintaining SOC 2 compliance is not merely a box-checking exercise for the annual audit; it is a fundamental pillar of modern organizational security. For many businesses, the most significant risk to information integrity is not an external threat actor, but the residual access left behind by former employees. Stale accounts provide a silent, unmonitored entry point into sensitive environments, often remaining active weeks or months after a departure.
System and Organization Controls (SOC 2) Type II reports place a heavy emphasis on logical access control, particularly how access is revoked when an individual's relationship with the organization ends. Failure to demonstrate a consistent, timely, and documented offboarding process is one of the most common reasons for an audit exception. Organizations must bridge the gap between HR actions and IT execution to ensure security and maintain trust.
The challenge lies in the complexity of modern IT ecosystems where access is spread across on-premises directories, cloud providers, and dozens of SaaS applications. A manual offboarding checklist is no longer sufficient to meet the rigorous evidence requirements of a SOC 2 audit. Automated offboarding is the necessary evolution for any compliance-focused organization.
Deciphering Logical Access Control: CC6.1 and CC6.7
SOC 2 criteria are structured around Trust Services Criteria (TSC). Two specific points of focus for employee termination are CC6.1 and CC6.7. These criteria demand that an organization protects its information assets through robust logical access security and that this access is removed when it is no longer required.
CC6.1 requires the implementation of logical access security software, infrastructure, and architectures. This means the tools used to manage access must be capable of enforcing the policies defined by the organization. If a policy states that access must be removed immediately upon termination, the infrastructure must support that speed and provide proof of the action.
CC6.7 focuses on the lifecycle of access, specifically the modification or removal of access when roles change or employment ends. Auditors look for a "termination sample," typically a selection of employees who left the company during the audit period. For each individual in the sample, the organization must provide timestamped evidence that all logical access was revoked in accordance with internal policy.

The Cost of Inefficiency: The Manual Offboarding Crisis
Manual offboarding processes are inherently prone to human error and significant delays. In many organizations, the trigger for offboarding is a manual email or a help desk ticket sent from HR to IT. This handoff introduces a critical delay where an account might remain active and vulnerable for several days.
The standard expectation for SOC 2 compliance is the revocation of access within 24 hours of termination. Manual workflows rarely achieve this consistently across every system. Common "control gaps" in manual processes include:
- Incomplete Revocation: IT may disable the primary Active Directory account but forget about secondary SaaS applications like Slack, GitHub, or AWS.
- Lack of Evidence: Even if access is revoked, there may be no centralized log capturing the exact time and date the action occurred.
- Non-Standard Processes: Different IT administrators may handle terminations differently, leading to inconsistent security postures across the organization.
These failures lead to audit findings that can jeopardize customer contracts and damage an organization’s reputation. Reliance on human memory for security tasks creates unnecessary operational risk.
HR-Triggered Automation: Closing the Control Gap
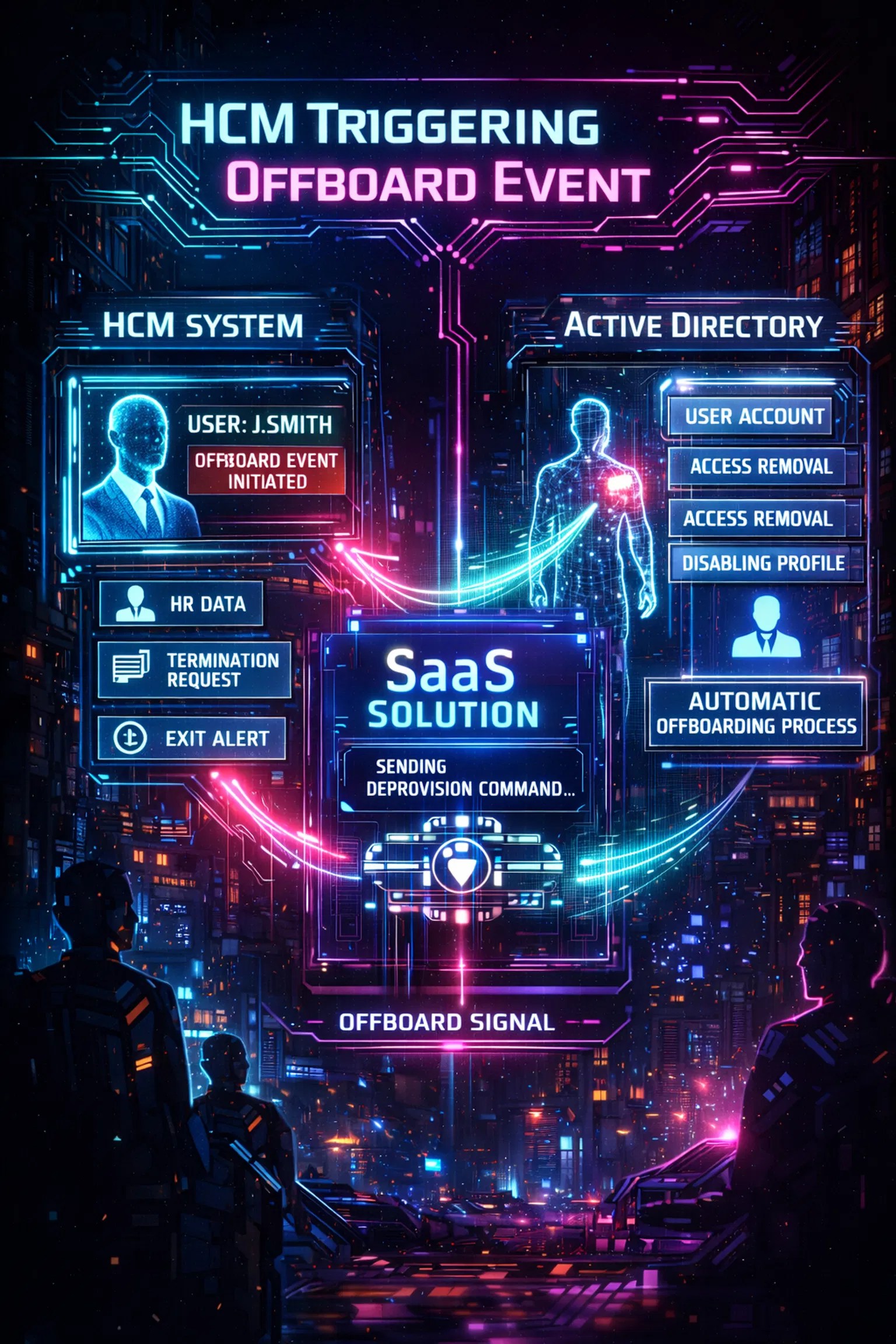
The most effective way to satisfy SOC 2 requirements is to treat HR as the authoritative source of truth. When an employee is marked as "terminated" in the Human Capital Management (HCM) system, it should trigger an immediate and automated chain of events across the IT landscape. This eliminates the delay caused by manual notifications.
Offboarder facilitates this through a platform that monitors HR systems for status changes. Once a termination is detected, the platform automatically initiates deprovisioning commands to Active Directory, Google Workspace, Microsoft 365, and other connected systems. This "HR-to-IT" bridge ensures that the 24-hour revocation window is met every single time, without exception.
Automation removes the burden of manual execution from lean IT teams. It ensures that security protocols are followed exactly as designed, providing a repeatable process that auditors can trust. Standardizing the offboarding lifecycle turns a complex, multi-team process into a seamless background operation.
Multi-Domain Support and Identity Matching
A significant hurdle in automated offboarding is managing users across multiple domains and disparate systems. An employee might have one username in a legacy on-premises domain and a different email alias for cloud-based SaaS tools. Without intelligent identity matching, automation can fail to identify and disable all associated accounts.
The platform must support multi-domain environments and flexible identity matching to be effective. Offboarder utilizes a cloud-native architecture paired with a lightweight on-prem agent to reach into any corner of the enterprise network. This ensures that whether an account exists in a local Active Directory or a remote cloud instance, it is accounted for and neutralized.
This comprehensive coverage is essential for SOC 2, as auditors look for "complete" termination of access. Partial offboarding: where some accounts are disabled while others remain active: is considered a control failure. A unified platform provides the visibility and control necessary to prevent these fragmented security states.
Audit-Ready Evidence: Turning Activity into Accountability
In a SOC 2 audit, "if it wasn't documented, it didn't happen." Auditors do not take your word for it; they require tamper-resistant, timestamped logs that serve as proof of compliance. Generating this evidence manually during an audit is a time-consuming and stressful process for IT and Compliance Managers.
Automated offboarding solutions solve this problem by generating comprehensive audit-ready evidence at the time of execution. For every termination, the platform captures:
- The exact time the termination was triggered in the HR system.
- The specific timestamp when access was revoked in each downstream system.
- The success or failure status of each deprovisioning task.
This evidence is stored in a centralized repository, ready to be exported for internal audit teams or external SOC 2 auditors. Having this data readily available reduces audit prep time from weeks to hours. Comprehensive evidence capture transforms daily security activities into long-term organizational accountability.

Risk Mitigation Beyond the Audit
While SOC 2 compliance is a powerful motivator, the primary goal of secure offboarding is risk mitigation. Terminated employees represent a unique threat profile; they possess deep knowledge of the organization’s systems and may have a motive for data exfiltration or sabotage. "Ghost accounts": active accounts belonging to former employees: are frequent targets for hackers looking for an undetected way into a network.
Automated offboarding significantly reduces the attack surface by minimizing the window of opportunity for unauthorized access. It ensures that credentials are invalidated before they can be exploited. This proactive stance is essential for organizations in highly regulated industries like FinTech and Healthcare, where data breaches carry heavy legal and financial penalties.
A secure offboarding process also demonstrates a commitment to governance and security maturity. It signals to partners, customers, and investors that the organization takes its custodial responsibilities seriously. High-stakes security requires high-precision execution.
Standardizing the Offboarding Lifecycle
Achieving SOC 2 compliance for logical access control requires more than a policy document; it requires a functional, verifiable system for removing access. Manual processes are too slow, too inconsistent, and too difficult to audit. Automation is the only viable path forward for organizations that need to scale while maintaining a strict security posture.
By implementing an HR-triggered, automated offboarding solution, organizations can:
- Ensure Timely Revocation: Meet the strict 24-hour window required by many compliance frameworks.
- Eliminate Manual Errors: Remove the risk of missed accounts or forgotten steps in the offboarding process.
- Simplify Audit Prep: Generate tamper-resistant evidence automatically for every termination.
- Reduce Operational Costs: Free up IT resources to focus on high-value projects instead of repetitive admin tasks.
Standardizing the offboarding lifecycle ensures that every departure is handled with the same level of rigor and security. Consistent execution is the foundation of a reliable compliance program.

Conclusion
SOC 2 compliance is a continuous journey of demonstrating control and accountability. Logical access revocation is a critical checkpoint on that journey. Organizations must move away from the "hope and help-desk" model of offboarding and embrace a technology-driven approach that prioritizes speed and proof.
The Offboarder platform provides the tools necessary to automate these critical workflows, bridging the gap between HR and IT. By integrating directly with your authoritative sources and downstream systems, we ensure that your offboarding process is not just compliant, but genuinely secure. Strong logging and automation help turn daily activity into long-term organizational accountability.
For organizations ready to eliminate the "control gap" in their termination process, the path forward is clear: automate the lifecycle, secure the environment, and provide the proof. Secure offboarding should be a silent, reliable constant in your security architecture.
Leave a Reply