Maintaining compliance in a modern IT environment requires more than a checklist. It requires a systematic approach to Identity and Access Management (IAM) that prioritizes the immediate removal of access when an individual leaves the organization. Manual deprovisioning processes often result in "control gaps," where terminated employees retain access to sensitive systems for days or weeks. This delay is a direct violation of major security frameworks and represents a significant operational risk.
Automating deprovisioning is no longer an optional luxury for IT teams. It is a fundamental requirement for meeting ISO 27001 and SOC 2 standards. This guide examines the technical requirements, compliance hurdles, and practical steps needed to transition from manual checklists to an automated, audit-ready offboarding workflow.
The Compliance Landscape: Why "Soon" Isn't Good Enough
Regulatory frameworks like SOC 2 and ISO 27001 focus heavily on logical access controls. Specifically, they require organizations to prove that access is granted only to authorized users and is revoked promptly upon termination.
A common failure during a SOC 2 audit occurs when an auditor compares HR termination dates against the actual timestamp of account deactivation in Active Directory or SaaS applications. If a gap exists, it is flagged as a control deficiency. Relying on manual tickets or human intervention introduces latency that leads to non-compliance. Why termination of access controls matters more than you think is a question of both security and legal obligation.

ISO 27001 and SOC 2 Requirements
- ISO 27001 Annex A.9.2.6: Requires that access rights of all employees and external party users to information and information processing facilities shall be removed upon termination of their employment, contract, or agreement.
- SOC 2 CC6.3: Specifies that the entity authorizes, modifies, or terminates access to relevant relevant information assets based on roles, responsibilities, or the nature of the changes.
To meet these standards, organizations must move away from ad-hoc processes. Automated deprovisioning ensures that the moment a status change occurs in the HR system, access removal begins across all connected environments. Consistency is the foundation of audit-readiness.
Identifying the Control Gap in Manual Offboarding
Manual offboarding is a fragmented process. It usually begins with an email from HR to IT, followed by the creation of a support ticket. An IT administrator then manually logs into various consoles: Active Directory, Google Workspace, AWS, and various SaaS platforms: to disable accounts one by one.
This process is inherently flawed for several reasons:
- Latency: Tickets sit in queues. If an employee is terminated on a Friday afternoon but the ticket isn't processed until Monday, the organization has been at risk for 48 hours.
- Inconsistency: An administrator might remember to disable the primary email account but forget the VPN access or a specific cloud database.
- Lack of Evidence: Manual processes rarely generate the tamper-resistant logs required for an audit. Proving when and who revoked access becomes a forensic exercise rather than a simple report.
Automating these steps eliminates the "control gap" by replacing human memory with programmatic triggers. Why secure offboarding matters is evidenced by the reduction of "zombie accounts" that remain active long after an employee has departed.
The Architecture of Automated Deprovisioning
An effective IAM automation strategy requires a seamless link between the "Source of Truth" (the HR system) and the "Target Systems" (IT infrastructure).
The process typically follows this logic:
- The Trigger: A status change in the HRIS (e.g., Workday, BambooHR, or Gusto) marks an employee as "Terminated."
- The Orchestrator: A platform like Offboarder detects this change and initiates a predefined workflow.
- The Action: The platform sends commands to disable accounts, revoke tokens, and remove group memberships across on-premises and cloud systems.
- The Verification: The system captures a success notification and logs the event for audit purposes.
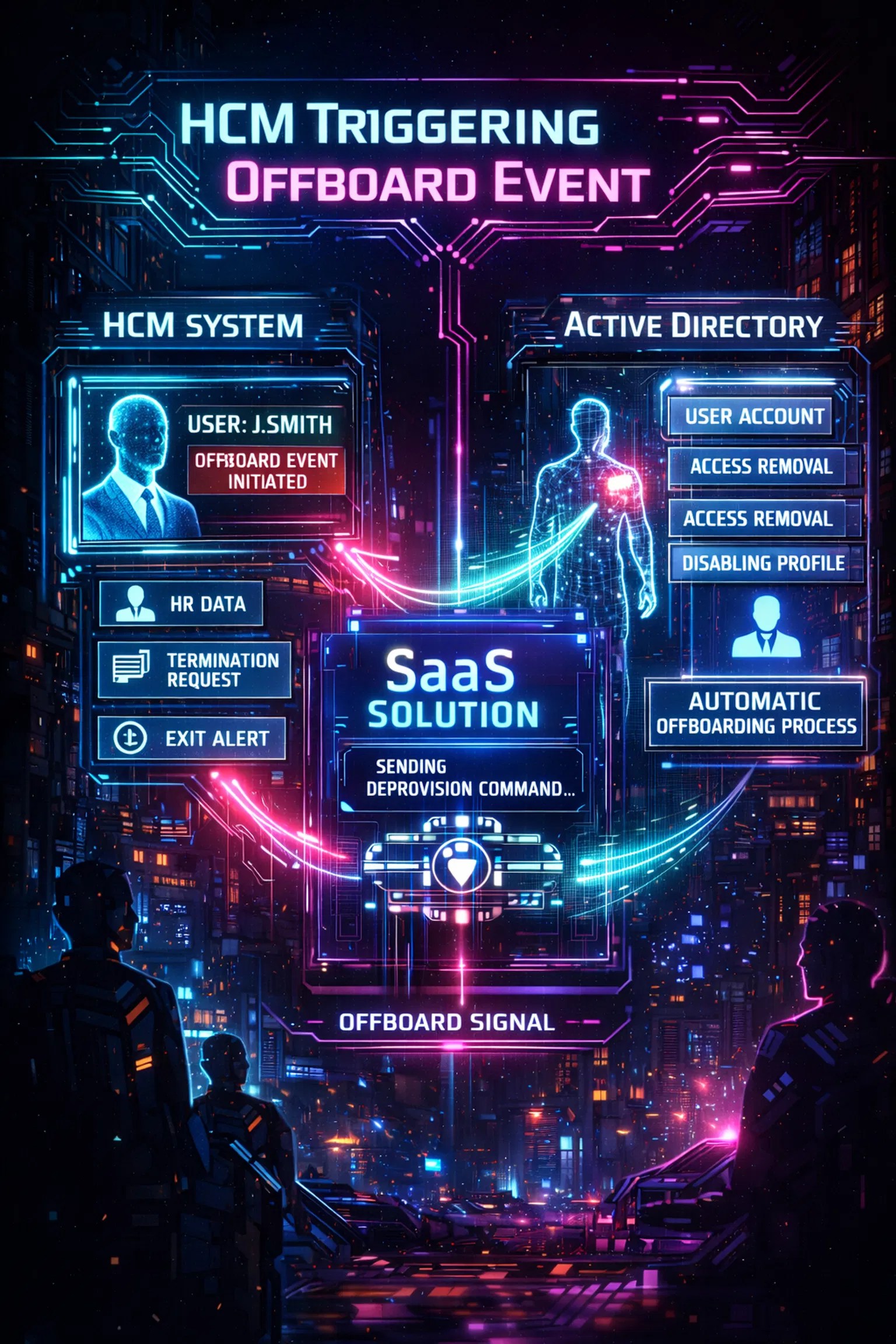
For organizations with hybrid environments, this architecture must bridge the gap between cloud-based HR tools and on-premises Active Directory. Utilizing a cloud-to-local agent allows for secure communication without opening dangerous firewall ports. This ensures that the Offboarder architecture remains secure while maintaining full control over local identity stores.
Essential Components to Automate
To achieve full IAM compliance, automation must extend beyond simple email deactivation. A comprehensive deprovisioning workflow should include:
1. Primary Identity Provider (IdP)
The first step is disabling the primary account in Active Directory, Azure AD, or Google Workspace. This acts as a "kill switch" for many integrated applications. However, it is not a complete solution, as some systems may retain active sessions or bypass SSO.
2. Multi-Factor Authentication (MFA)
Failing to revoke MFA tokens is a common security oversight. If an account is disabled but the MFA device remains registered, a malicious actor (or a disgruntled former employee) might find alternative pathways to re-enable access. Automation should include the immediate clearing of registered MFA devices.
3. VPN and Remote Access
Remote access represents the highest risk level. Automated deprovisioning must terminate active VPN sessions and disable certificates immediately. In a remote-first world, leaving a VPN connection active for a terminated user is an unacceptable vulnerability.
4. SaaS and Cloud Application Access
Shadow IT and disconnected SaaS platforms are audit nightmares. An automated system should provide integration with major SaaS platforms to ensure that access to CRM, ERP, and DevOps tools is revoked simultaneously with the primary IdP.

Turning Activity into Accountability: Audit-Ready Logging
In the eyes of a security auditor, if an action wasn't logged, it didn't happen. Automated deprovisioning platforms provide a centralized repository of "evidence capture."
Every automated action should generate a log entry containing:
- The exact timestamp of the status change in HR.
- The timestamp of the account deactivation in each target system.
- The status of the operation (Success/Failure).
- The specific identity of the system that performed the action.
This level of detail turns a complex audit into a simple reporting task. Instead of gathering screenshots from ten different systems, the IT team can present a single, unified report demonstrating 100% compliance with access removal policies. This is why identity governance tools exist: to transform technical tasks into verifiable governance.
Implementation Roadmap: Moving Toward Automation
Transitioning to automated deprovisioning does not have to be a disruptive "big bang" event. A structured approach allows for risk mitigation during the rollout.
- Define the Policy: Document exactly what "deprovisioning" means for your organization. Which systems are critical? What is the maximum allowable latency?
- Audit the Environment: Identify all systems where user accounts are created. Distinguish between those that support SSO and those that require direct management.
- Choose a Trigger: Ensure your HR data is clean. Automated systems rely on accurate "Termination Dates." If HR data is incorrect, the automation will be incorrect.
- Deploy an Agent-Based Solution: For hybrid setups, implement a secure agent to connect cloud-based triggers to local Active Directory instances. This is often the most critical step in automated deployment.
- Test and Refine: Run the automation in "notification-only" mode for the first few departures to ensure the logic holds before enabling full account deactivation.
Organizations that implement these steps find that they spend less time on manual administration and more time on high-value security projects. The shift from reactive to proactive IAM management is a hallmark of a mature security organization.
Mitigating Operational Risk
Beyond compliance, automated deprovisioning is a powerful tool for risk reduction. Insider threats are significantly heightened during the window immediately following a termination. Disgruntled employees may attempt to download proprietary data or disrupt services if their access is not revoked instantly.
Automation removes the "human element" from this critical security junction. It ensures that the removal of access is a neutral, systematic process that occurs without fail. By standardizing this procedure, the organization treats every departure with the same level of rigor, regardless of the circumstances.

Conclusion: The Path Forward
The complexity of modern IT environments makes manual IAM management unsustainable. As organizations scale, the number of "points of failure" in a manual offboarding process grows exponentially.
Automating deprovisioning through a dedicated platform like Offboarder allows IT teams to satisfy auditors, secure sensitive data, and eliminate the burden of repetitive manual tasks. By aligning IT actions directly with HR triggers, organizations can achieve a level of IAM compliance that is both robust and scalable.
Securing the exit is just as important as securing the entrance. Establishing a tamper-resistant, automated workflow ensures that when an employee leaves, their access leaves with them: immediately and completely.
For more information on how to streamline your security posture, visit our implementation guide or learn more about our story. Strong logging helps turn activity into accountability.

Leave a Reply