![[HERO] Why Employee Offboarding Automation Will Change the Way You Manage IAM Compliance](https://i0.wp.com/cdn.mar4blism.com/EwocCqA0BR3.webp?ssl=1)
Managing Identity and Access Management (IAM) compliance has historically been a manual, fragmented process. For most organizations, the transition of an employee out of the company triggers a cascade of emails, tickets, and spreadsheets. This manual approach creates a significant "control gap" between the moment an employee departs and the moment their digital identities are actually revoked.
In a modern security landscape, this delay is no longer just an operational inefficiency; it is a critical compliance failure. Automated offboarding fundamentally shifts the paradigm by transforming access termination from a reactive task into a proactive, governed security control. By integrating HR triggers directly with IT systems, organizations can ensure that compliance is a byproduct of the process, not an afterthought.
The Compliance Crisis of Manual Offboarding
Regulatory frameworks such as ISO 27001, SOC 2, and HIPAA mandate strict controls over logical access. Specifically, they require evidence that access to sensitive systems is revoked "timely" upon a change in employment status. In a manual environment, proving "timeliness" is nearly impossible because the paper trail is often broken or inconsistent.
When an organization relies on human intervention to disable accounts across Active Directory, SaaS applications, and internal databases, the risk of human error escalates. A single missed account can lead to an "orphaned account," which becomes a prime target for credential-based attacks. From an auditor's perspective, an orphaned account is not just a security risk; it is a direct violation of access control policies that can jeopardize certification.
The primary challenge lies in the disconnect between the Human Resources Information System (HRIS) and the IT infrastructure. Without a synchronized link, IT often remains unaware of a termination until hours or days after the event. This visibility gap represents the greatest threat to IAM compliance today.
Closing the "Access Gap" with Real-Time Triggers
Automated offboarding platforms, such as Offboarder, eliminate the access gap by establishing a direct communication line between the HCM system and the IAM environment. The moment a termination is finalized in HR, a deprovisioning command is issued across the entire stack.
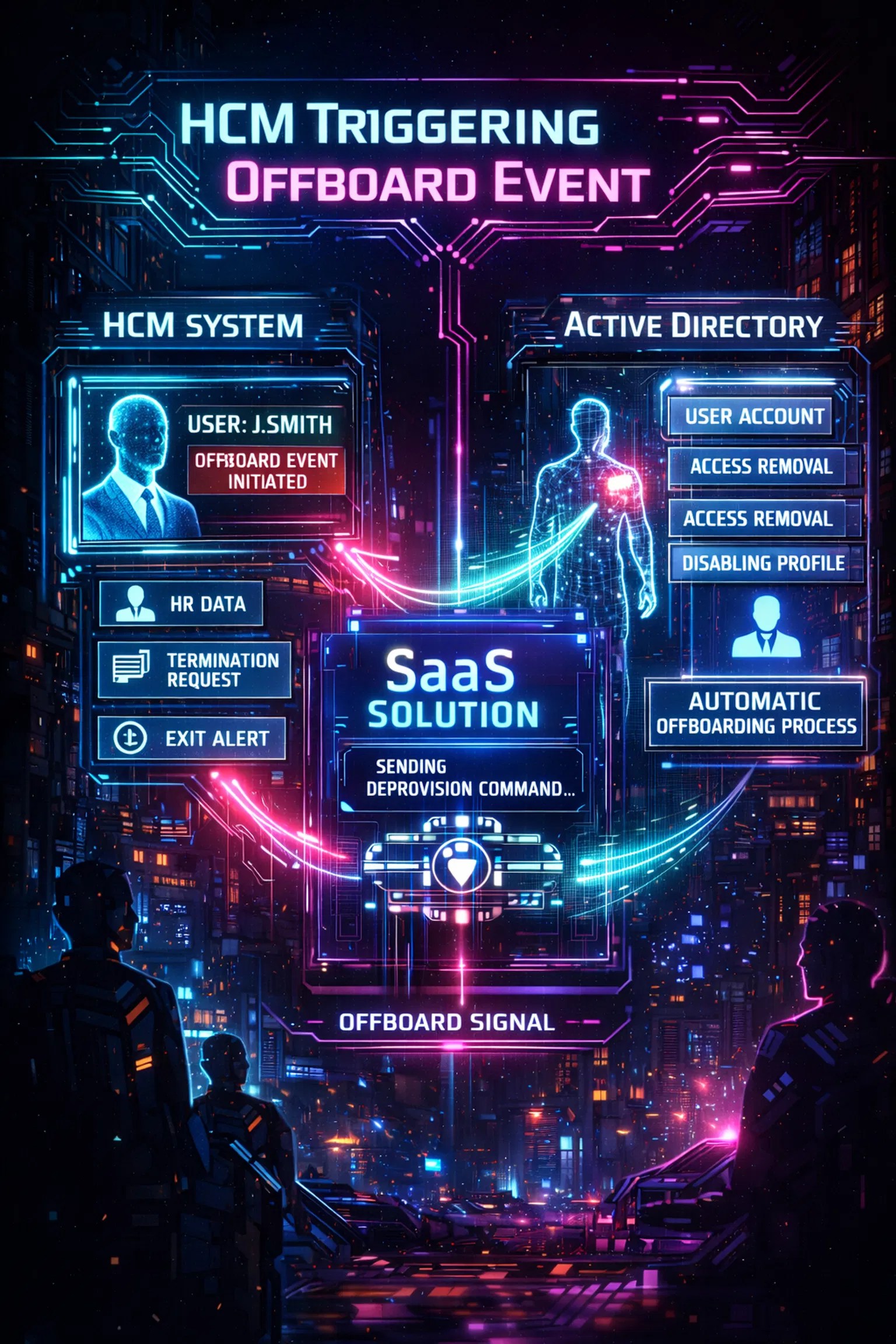
This shift from manual ticketing to API-driven automation ensures that access removal happens in minutes, not days. This speed is a core requirement for maintaining security and compliance in high-stakes industries. When revocation is instantaneous, the window of opportunity for unauthorized access is effectively closed, drastically reducing the organization's operational risk.
Furthermore, automation ensures consistency. In a manual process, one administrator might follow a checklist diligently, while another might overlook a specific SaaS application. Automation applies the same set of logic to every departure, ensuring that no account is left active by mistake.
Transforming Activity into Audit-Ready Evidence
One of the most significant changes automation brings to IAM is the concept of "evidence capture." Auditors require more than just a statement that an account was disabled; they require tamper-resistant proof of when the action occurred and who (or what system) authorized it.
Manual logs, which are often reconstructed after the fact from various system exports, are difficult to maintain and easy to challenge. Automated offboarding platforms generate immutable audit trails for every offboarding event. These logs document the initial HR trigger, the specific accounts disabled, and the success confirmation from each target system.
By centralizing this data, the platform turns a complex auditing chore into a simple reporting task. Instead of spending weeks gathering evidence for a SOC 2 audit, security teams can provide a consolidated report that demonstrates 100% compliance with access revocation policies. Strong logging helps turn activity into accountability.
Strategic Integration: Connecting the Cloud to On-Premises
Modern IAM compliance is complicated by hybrid environments. While many organizations have moved to the cloud, critical assets often remain within on-premises domains. Bridging the gap between these environments is essential for comprehensive identity governance.

Offboarder’s architecture addresses this by utilizing a secure agent that connects on-premises domains to a cloud-based admin portal. This allows for the automated disablement of Active Directory users alongside SaaS account deprovisioning. This holistic approach ensures that compliance is maintained across the entire digital estate, regardless of where the data resides.
The ability to manage both cloud and on-premises identities from a single pane of glass provides the level of oversight that modern frameworks like ISO 27001 demand. It ensures that the "logical access" controls are applied universally, leaving no dark corners for security vulnerabilities to hide.
Reducing Operational Risk for Lean Teams
Security and IT teams are often overstretched, leading to "technical debt" in the form of incomplete offboarding. Manual offboarding is a high-volume, low-value task that consumes hours of administrative time. When teams are busy, these tasks are often deprioritized, leading to the accumulation of residual privileges.
Automation reclaims this time, allowing teams to focus on strategic security initiatives rather than repetitive administrative work. By streamlining the process, organizations can scale their operations without a corresponding increase in headcount. This is particularly valuable for fast-growing companies that must maintain rigorous security standards while managing high employee turnover or rapid hiring cycles.

A streamlined path forward is essential for maintaining a strong security posture in a competitive market. By removing the "human factor" from the critical path of access revocation, the platform reduces the likelihood of insider threats: whether malicious or accidental. This reduction in operational risk translates directly into a more resilient organization.
The Future of IAM Compliance Governance
The shift toward automation is not merely a trend; it is a fundamental evolution of how organizations handle digital identity. In the past, IAM was focused on "Access Management": getting people into the systems they needed. Today, the focus has shifted to "Access Governance": ensuring that people are removed from systems the moment they no longer need access.
This proactive stance on governance is what separates secure organizations from those that are merely "compliant on paper." True compliance requires a system that is tamper-resistant, verifiable, and fast. Manual processes cannot meet these requirements at scale.
As regulatory bodies continue to tighten their requirements around data protection and privacy, the importance of automated offboarding will only grow. Organizations that fail to adopt these technologies risk not only audit failures but also significant security breaches that could have been easily prevented.
Key Benefits of Automating IAM Compliance
- Elimination of Human Error: Standardized workflows ensure that every step of the deprovisioning process is followed every time.
- Immediate Risk Mitigation: Revoking access the moment a termination is recorded in HR minimizes the window for data exfiltration.
- Centralized Visibility: A single portal provides a clear overview of the status of all offboarding tasks across the organization.
- Audit-Ready Documentation: Immutable logs provide the evidence needed for ISO 27001 and SOC 2 audits with minimal effort.
- Scalability: The system handles increased volumes of departures without requiring additional IT resources.
Implementing an automated solution is a strategic investment in the long-term security of the business. Organizations should view offboarding not as an HR checklist, but as a primary security control that must be hardened against failure.
Taking the Next Step Toward Secure Offboarding
Transitioning from manual to automated offboarding does not have to be a complex undertaking. With the right platform, the implementation process can be straightforward, moving from a fragmented state to a unified governance model in a matter of weeks.
For startups and enterprise organizations alike, the priority must be on strengthening logical access controls. The risks associated with manual offboarding: orphaned accounts, audit findings, and potential breaches: far outweigh the cost of implementing a dedicated automation solution.

By choosing to automate, you are not just checking a box for an auditor; you are building a more secure, efficient, and accountable organization. The future of IAM compliance is automated, and the tools to achieve it are available today.
Explore how Offboarder can transform your compliance strategy by visiting our overview page or reaching out for a consultation. Managing access shouldn't be a gamble: automate your offboarding and secure your perimeter once and for all.
Comprehensive automation ensures that every departure is handled with the precision and speed that modern security requires. High-quality logging and real-time execution turn identity management into a powerful asset for business continuity and risk reduction.

Leave a Reply