Identity and Access Management (IAM) has evolved from a back-office administrative task into the cornerstone of modern cybersecurity. In an era where the traditional network perimeter has dissolved, identity is the primary line of defense. Organizations must ensure that only the right people have the right access to the right resources at the right time.
However, many organizations focus heavily on the "onboarding" and "access" portions of the lifecycle while neglecting the most critical security event: the termination of access. Automated offboarding is no longer a luxury for large enterprises; it is a fundamental requirement for any business aiming to meet rigorous compliance standards and mitigate operational risk.
The Critical Role of IAM in the Modern Enterprise
IAM is a framework of policies and technologies designed to ensure that the proper users have the appropriate access to technology resources. It encompasses the entire lifecycle of a user identity, from the initial creation of credentials to the eventual revocation of all permissions.
The primary challenge for growing organizations is the sheer volume of SaaS applications and decentralized systems. Manual management leads to "identity debt," where orphaned accounts and excessive permissions accumulate over time. This creates a significant "control gap," leaving the organization vulnerable to unauthorized access and data breaches.
To achieve a resilient security posture, the IAM strategy must move beyond simple password management. It must incorporate automated governance that scales with the business. For a deeper look at why these tools are necessary, organizations should evaluate why identity governance tools exist to bridge the gap between IT operations and security requirements.
The Pillars of Identity and Access Management
A robust IAM solution is built upon four fundamental pillars. Each pillar must function correctly to maintain the integrity of the organizational environment.
- Authentication: This verifies that a user is who they claim to be. Modern standards require Multi-Factor Authentication (MFA) and Single Sign-On (SSO) to centralize the login process.
- Authorization: Once authenticated, the system must determine what actions the user is permitted to perform. This is typically managed through Role-Based Access Control (RBAC), ensuring the principle of least privilege.
- Administration: This involves the management of the identity lifecycle, including the creation, modification, and deletion of user accounts.
- Auditing and Compliance: The system must provide a tamper-resistant trail of who accessed what and when. This evidence is crucial for security and compliance audits like SOC 2 and ISO 27001.
Failure in any of these pillars, particularly administration and auditing, results in a loss of governance that is difficult to remediate manually.
The Lifecycle Vulnerability: Why Offboarding Fails
The most significant vulnerability in the IAM lifecycle is the "termination gap." This is the period between an employee’s departure and the actual revocation of their access across all corporate systems.
Manual offboarding processes are inherently flawed. They rely on human communication between HR and IT, which is often delayed or inconsistent. If an IT administrator misses a single application or forgets to disable a local account, a "zombie account" is created. These orphaned identities are prime targets for attackers and disgruntled former employees.
The business impact of failed offboarding includes:
- Security Breaches: Former employees retaining access to sensitive customer data or intellectual property.
- Compliance Failure: Auditors view active accounts for terminated employees as a direct violation of logical access controls.
- Financial Waste: Organizations continue to pay for SaaS licenses for users who are no longer with the company.
Automated offboarding resolves these issues by replacing manual checklists with programmatic execution.
Achieving Compliance with Automated Offboarding
For companies pursuing ISO 27001 or SOC 2 certification, the timely removal of access is a non-negotiable requirement. Compliance frameworks demand proof that access is revoked "immediately" or within a strictly defined window: often 24 hours.
Automated offboarding provides the necessary evidence capture to satisfy auditors. When a termination is triggered in the Human Resources Information System (HRIS), the platform automatically executes deprovisioning commands across the entire tech stack. This creates a documented audit trail that shows the exact timestamp of access removal.
Without automation, providing this level of proof requires hours of manual log collection and spreadsheet tracking. By implementing a standardized process, the platform ensures that termination of access controls are applied consistently every time, reducing the risk of human error and audit findings.
The Architecture of Automated Deprovisioning
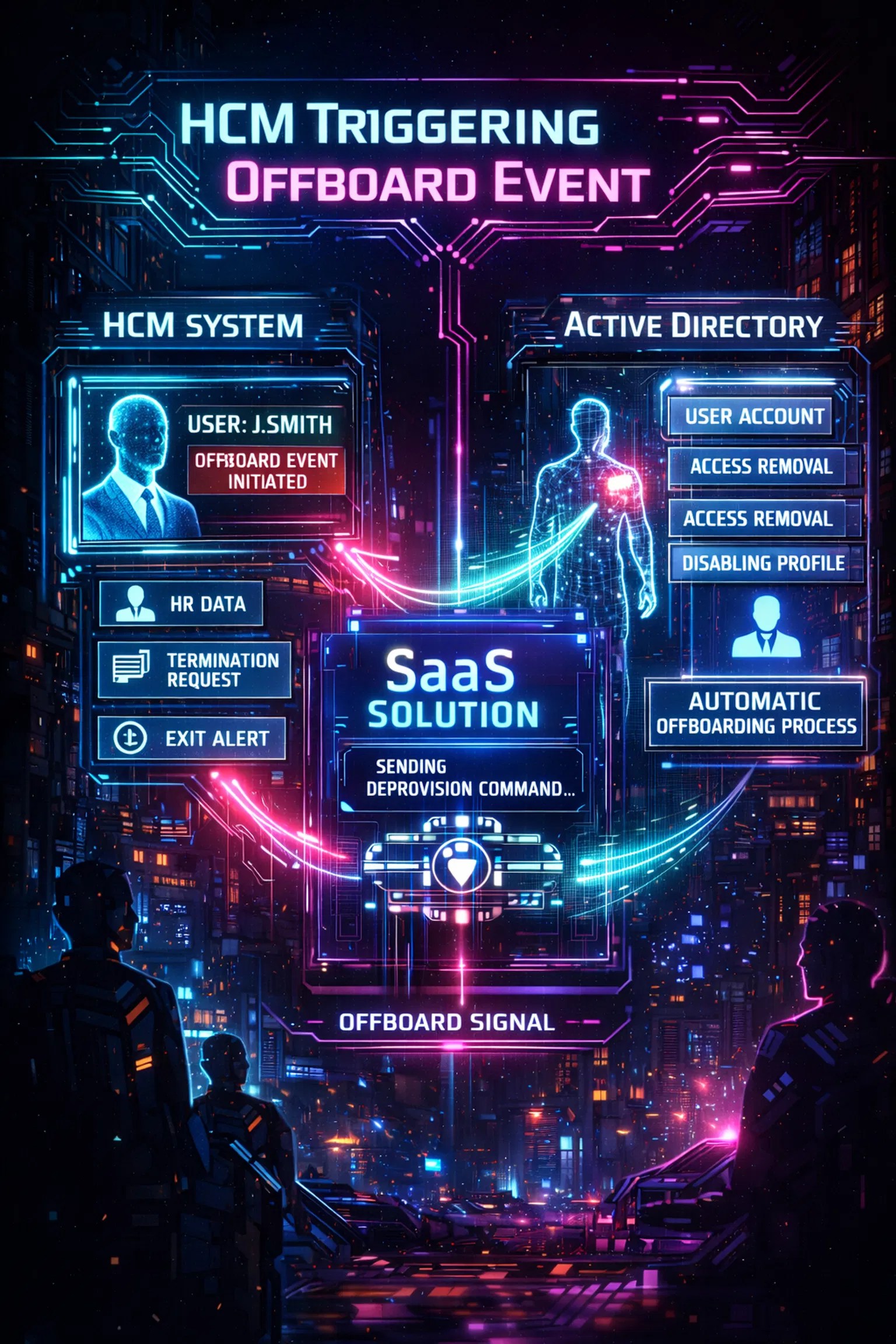
A successful IAM automation strategy requires a seamless flow of data between HR systems and IT infrastructure. The "source of truth" should always be the HRIS or HCM system. When an employee's status changes to "terminated," this event must trigger a downstream reaction.
The architecture typically involves:
- The Trigger: An HR-triggered event (e.g., in Workday, BambooHR, or Gusto).
- The Orchestrator: A platform like Offboarder that receives the signal and interprets the required actions.
- The Execution: API calls or agent-based commands that disable accounts in Active Directory, Google Workspace, and various SaaS applications.
- The Verification: A success notification and log entry confirming that access has been removed.

Using an HR-triggered offboarding model ensures that IT is never out of the loop. It removes the need for "hope-based" security, where IT departments hope they were notified of every departure.
Reducing Operational Risk and Technical Debt
Operational risk is often the result of "technical debt" accumulated through lean teams trying to manage complex systems. When IT teams are overworked, security tasks that don't yield immediate visible results: like cleaning up old accounts: are often deprioritized.
The platform mitigates this risk by automating the mundane. This allows the security team to focus on high-value activities like threat hunting and architecture design rather than manual password resets or account deactivations.
Furthermore, the consistency provided by automation prevents the configuration drift that occurs when different administrators use different offboarding methods. A unified approach ensures that every departure is handled with the same level of rigor, regardless of the employee's role or seniority. This level of governance is essential for maintaining a clean and secure environment.
Key Features to Look for in an IAM Offboarding Solution
When evaluating IAM solutions for offboarding, organizations should prioritize functionality over flashy interfaces. The goal is risk reduction and audit readiness.
- Native Integrations: The solution must connect directly to your HRIS and your primary identity providers (like Active Directory or Okta).
- Evidence Logs: Every action taken by the platform must be logged with high fidelity for compliance reporting.
- Customizable Workflows: The ability to define different offboarding paths for different departments (e.g., immediate lockout for IT staff vs. delayed mailbox access for sales managers).
- Scalability: The platform must handle high volumes of changes without manual intervention.
- Secure Connectivity: For hybrid environments, look for solutions that use secure agents to bridge the gap between cloud portals and on-premises domains.
The implementation of these features should be straightforward, enabling the organization to realize value quickly without months of professional services.

The Strategic Value of Speed and Consistency
In the context of cybersecurity, speed is a defensive metric. The faster access is revoked, the smaller the window of opportunity for an insider threat or a compromised account to be exploited.
Consistency is equally important. If 95% of employees are offboarded correctly but 5% are missed due to manual errors, the organization remains at risk. An automated system ensures 100% consistency. This predictability is what transforms a chaotic IT process into a streamlined security control.
By prioritizing secure offboarding, businesses protect their most valuable assets: their data and their reputation. Automated tools provide the "proof" that security policies are being followed in practice, not just on paper.
Conclusion: Setting the Standard for Identity Governance
Identity and Access Management is no longer just about giving people access; it is about managing the risk associated with that access throughout its entire lifecycle. Automated offboarding is the final, and perhaps most critical, piece of that puzzle.
For organizations operating in regulated industries or those simply looking to harden their security posture, transitioning from manual to automated deprovisioning is an essential step. It eliminates the control gaps that lead to breaches, ensures compliance with international standards, and reduces the operational burden on IT teams.
Effective IAM requires a commitment to consistency, speed, and auditability. By leveraging specialized platforms like Offboarder, companies can ensure that when an employee leaves, their access leaves with them: immediately, completely, and verifiably. Strong automation turns activity into accountability.


Leave a Reply